The original Gebrüder Ottenheimer wove cotton and linen. This project weaves isolated communication channels into a secure fabric. The metaphor was not planned. It was inherited.
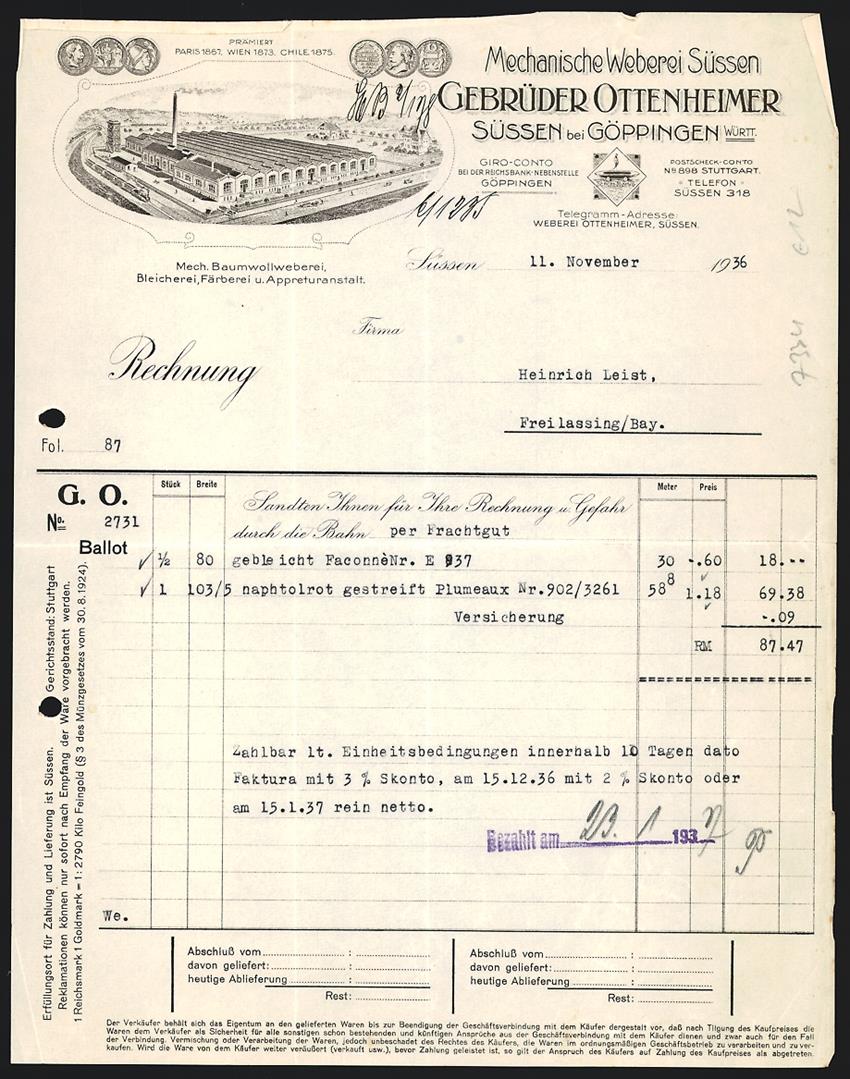
In 1862, Salomon and Joseph Ottenheimer founded a cotton and linen weaving mill in Jebenhausen, Württemberg. Mechanische Weberei Süßen, Gebrüder Ottenheimer. The mill won prizes in Paris, Vienna, and Chile. In December 1937, the family was forced to sell. Alfred Ottenheimer died in June 1938. His wife Luise was deported to Riga-Jungfernhof in December 1941.
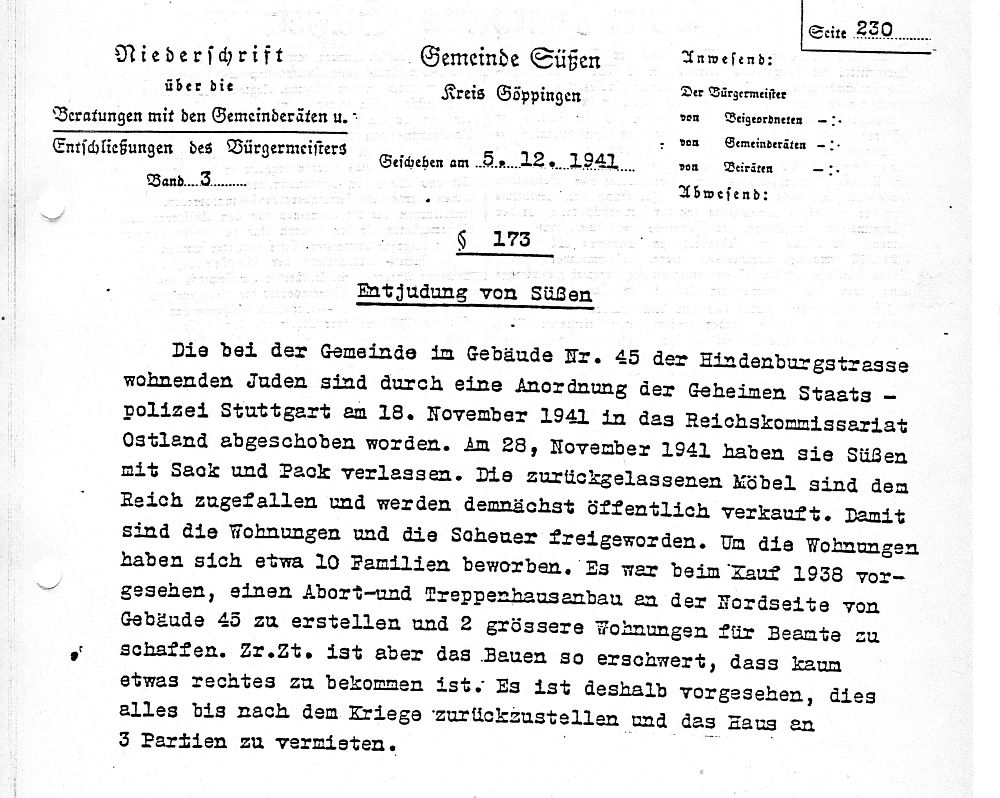
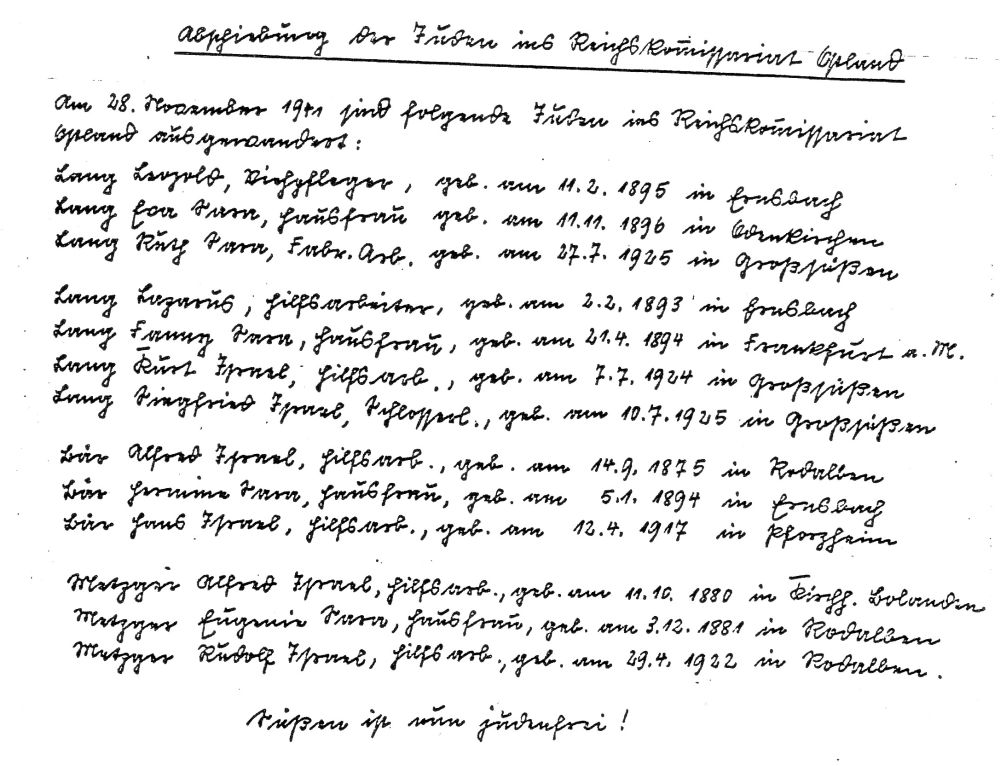
On 5 December 1941, the Süßen municipal council recorded §173: Entjudung von Süßen — the de-Jewification of Süßen. The Gestapo Stuttgart had ordered the deportation of the town's remaining Jews to the Reichskommissariat Ostland on 18 November. Their furniture was seized and sold publicly. Ten families applied for the vacated housing.
The handwritten deportation list ends with an exclamation: Süßen ist nun judenfrei!
The name Gebrüder Ottenheimer is not a brand exercise. It is a commitment to remember what was taken, and to build with the care that memory demands.
The Austrian Emperor
The agentic AI market has produced a dominant open-source platform built on the perspective of an absolute authority with absolute visibility into everything, secured by a single golden key. Those who remember Austrian history may recognize the pattern from neo-absolutist state secret services, which built a centralized espionage card index for surveillance of Vienna residents 1849–1868. OpenClaw, over 300,000 GitHub stars, consolidates access to all of a user's encrypted messaging channels behind a single static authentication token, in a single process, with no channel isolation, no credential rotation, no audit trail for agent actions, and no skill sandboxing. The project has accumulated 29 GitHub Security Advisories in three months of existence, including a one-click remote code execution vulnerability that exposed over 220,000 instances. Its skills marketplace had a 20% malware rate within weeks of launch.
The project's own security lead has publicly stated that fixing the architecture requires "deep architectural changes to how untrusted multi-agent memory and prompting are handled."
OpenAI acqui-hired OpenClaw's creator. Nvidia built a security wrapper around it. Neither action addresses the architectural failure. The market response has been to build locks for a door made from toilet paper.
The Architecture
Systems that survive persistent adversarial pressure are distributed, locally authoritative, isolated by channel, and designed so that compromise of one component cannot cascade to another. Centralised coordination points — a single token, a single gateway, a single process — are the vulnerability.
Wirken applies these principles to the agent orchestration problem.
Each messaging channel runs its own isolated adapter process with its own scoped credential. There is no single token that controls everything. Compromise of one channel cannot cascade to another. This isolation is enforced at compile time by Rust's type system. Each adapter is generic over a zero-sized channel marker type. A Telegram adapter holds a SessionHandle<Telegram> — a type that cannot be constructed by, converted to, or accessed from a Discord adapter because the type parameter is sealed. The compiler rejects cross-channel access before the code can run. It is not a runtime permission check that can be bypassed. It is a type constraint that eliminates the vulnerability class entirely.
All credentials are encrypted at rest with XChaCha20-Poly1305, keyed from the operating system's keychain. Decrypted secrets are wrapped in Rust's SecretString type, which does not implement Display, Debug, Serialize, or Clone. The compiler rejects any attempt to log, print, serialize, or copy a decrypted credential. The only access path returns a short-lived reference that cannot outlive the secret. When the value goes out of scope, its memory is zeroed. This is not a policy that developers must remember to follow. It is a property the compiler enforces on every code path. Credentials rotate on a configurable schedule and expire. There are no static forever-tokens.
Every agent action — every message read, every message sent, every tool invocation, every file access, every network request — is logged to an append-only, hash-chained audit ledger before execution. The user can query it: what did my agent do today? The hash chain is independently verifiable. Tampering is detectable.
Skills from the OpenClaw ecosystem work on day one — the majority are markdown instruction files that require no compilation or migration. Code skills run in sandboxed containers. New skills target WebAssembly with deterministic resource limits.
Rate limiting applies uniformly, including on localhost connections. There is no loopback exemption.
The system ships as a single static Rust binary. No npm. No node_modules. No runtime dependencies.
What Ships Today
The repository contains a Cargo workspace of independent crates covering the full architecture: encrypted credential vault, append-only audit log with hash chain verification, Cap'n Proto IPC with Ed25519 adapter authentication, gateway core with routing, sessions, permissions, and rate limiting, channel adapters with compile-time isolation, an agent runtime with LLM integration and tool execution, a CLI with a three-step setup wizard, and systemd/launchd service installation. Multiple channels run simultaneously as separate processes. Every step audited.
This is not a finished product. It is a foundation with the security architecture built in from the first commit, not bolted on after the first breach. We are publishing it now because the architecture should be examined, challenged, and improved by people who understand what is at stake when an Emperor's autonomous agents are being given access to your private communications.
MIT licensed. Contributions, criticism, and scrutiny are welcome.